Few domains demonstrate fintech product engineering more clearly than payments, where system design is driven by scale, regulation, and reliability constraints. McKinsey’s 2025 report on the payments industry notes that global payments revenue is projected to grow from $2.5 trillion in 2024 to $3.0 trillion by 2029, reflecting the increasing scale and complexity of modern payment ecosystems.
Behind every transaction is a product engineered to manage compliance requirements, fraud prevention, system resilience, and peak transaction volumes simultaneously. These requirements call for a level of specialized expertise beyond traditional software development.
Fintech product engineering is the discipline that bridges those requirements. It identifies legal frameworks, financial data integrity, and security architecture as the main technical constraints at the start of product development. These constraints influence all architectural decisions, from database design to API design and deployment topology.
To successfully supply regulated financial products, you need to have a good awareness of the basic components, major difficulties, best practices, applicable technologies, and effective team structures.
Content:
- Definition of Fintech Product Engineering
- Core Components
- Engineering Challenges
- Best Practices
- Technology Stack
- Fintech Product Engineering Team
- Use Cases
- How to Choose a Fintech Product Engineering Partner
Definition of Fintech Product Engineering
Fintech product engineering is the practice of designing, building, and operating software products within the regulatory and security constraints of the financial services industry. It spans architecture design, payment system integration, compliance implementation, fraud prevention, and data management. These are treated as interconnected engineering concerns rather than separate development phases.
The distinction from general software development becomes apparent at the infrastructure level. A typical web application can handle errors by retrying and informing the user; a payment processing system must provide exactly-once transaction execution, maintain tamper-evident audit trails, and achieve five-nines availability because downtime has regulatory reporting obligations and direct financial loss.
The 2026 McKinsey research on the next era of fintech highlights that worldwide fintech sales were around $650 billion in 2025 and may climb to about $2 trillion by 2030. So, resilient, compliant engineering infrastructure is a core prerequisite for sustained expansion in the industry.
Domain-specific failure modes demand domain-specific engineering expertise. Missed Strong Customer Authentication logic results in non-compliance with PSD2. An incorrectly scoped PCI DSS cardholder data environment results in a failed audit. A race condition in a ledger update produces a financial discrepancy that requires regulatory disclosure.
These outcomes stem from architectural decisions teams must make correctly from the first sprint, reinforcing the need to treat fintech product engineering as a dedicated discipline.
Core Components of Fintech Product Engineering
A production-ready financial product is an ensemble of interconnected components, each carrying its own set of technical and regulatory requirements. The table below summarises the five core areas and their expected outcomes:
| Component | Key Capabilities | Business Outcome |
| Product Architecture | Microservices, event-driven design, API-first | Scalability, loose coupling, rapid iteration |
| Payment Systems | Real-time processing, multi-rail routing, reconciliation | Low latency, transaction accuracy, settlement reliability |
| Security and Fraud | ML anomaly detection, tokenisation, 3DS2 | Fraud rate reduction, chargeback management |
| Compliance-by-Design | PCI DSS scoping, PSD2/SCA, GDPR data residency | Audit-readiness from sprint zero |
| Data Architecture | Event sourcing, immutable ledgers, BI pipelines | Accurate reporting, regulatory auditability |
Product Architecture and System Design
Event-driven, microservices architectures are well suited to fintech products because financial workflows require complete traceability and fault isolation: every state change, be it a debit instruction, a KYC decision or a settlement confirmation, is an event that needs to be recorded, replayed and auditable (by regulators or internal risk teams on demand). Tightly connected services break this paradigm, making it difficult to identify causality and hard to replay individual event streams in isolation.
Infrastructure decisions carry direct compliance implications from the point of provisioning. Cloud environments require PCI DSS-scoped network segmentation, DORA Article 6 resilience testing, and GDPR-compliant data residency configurations before any application workload is deployed.
Treating these as post-launch additions creates expensive retrofit programmes while embedding them in the infrastructure-as-code templates from day one is both more reliable and significantly cheaper to maintain.
Payment Processing Infrastructure
In fintech products, payment systems have limits that typical online services don’t have to handle. Real-time payment processing needs sub-200ms end-to-end latency, idempotency keys to avoid double charges from network retries and daily reconciliation pipelines that balance internal ledgers against scheme settlement reports.
Multi-rail routing (the option to choose between SEPA, Faster Payments, SWIFT, or card networks depending on transaction type, cost, and availability) adds a layer of state management complexity that developers new to payment infrastructure sometimes underestimate.
Security and Fraud Prevention Systems
PCI DSS compliance specifies the minimum standard: No cardholder data should be seen in application logs, encryption keys should be controlled in hardware security modules, and cardholder data environments should be network-segmented from all other systems. Fraud prevention goes beyond compliance duties, as it incorporates ML scoring models trained on transaction velocity, device fingerprints and behavioural cues to identify abnormalities in real time.
3D Secure 2 integration, payment tokenisation, and biometric authentication are now baseline requirements for consumer-facing payment products, and the financial and reputational cost of a breach makes this investment straightforward to justify.
Compliance-by-Design Frameworks
Compliance-by-design requires that all architectural and engineering decisions account for applicable regulatory frameworks from the outset of development. This applies to data storage location, API structure, access control models, and logging formats. As a result, compliance is embedded from the first sprint rather than addressed in a dedicated post-development phase.
EU-regulated fintech products typically operate under PSD2/PSD3 for payment services authorisation, GDPR for personal data handling, DORA for operational resilience (in force since January 2025), MiCAR for crypto-asset products, and PCI DSS for any environment that processes, stores, or transmits card data.
Data Architecture and Financial Reporting Systems
Financial data serves both operational and evidentiary purposes, which requires engineering decisions that go beyond standard database design. Immutable ledgers, event-sourced audit logs, and automated reconciliation pipelines are production engineering requirements: regulators can request transaction histories covering multi-year periods, and the system must produce accurate, complete responses to those requests on short notice.
Analytics pipelines for regulatory reporting, AML monitoring, and internal risk management must also be designed for correctness before performance, given the consequences of inaccurate financial reporting.
Fintech Product Engineering Challenges
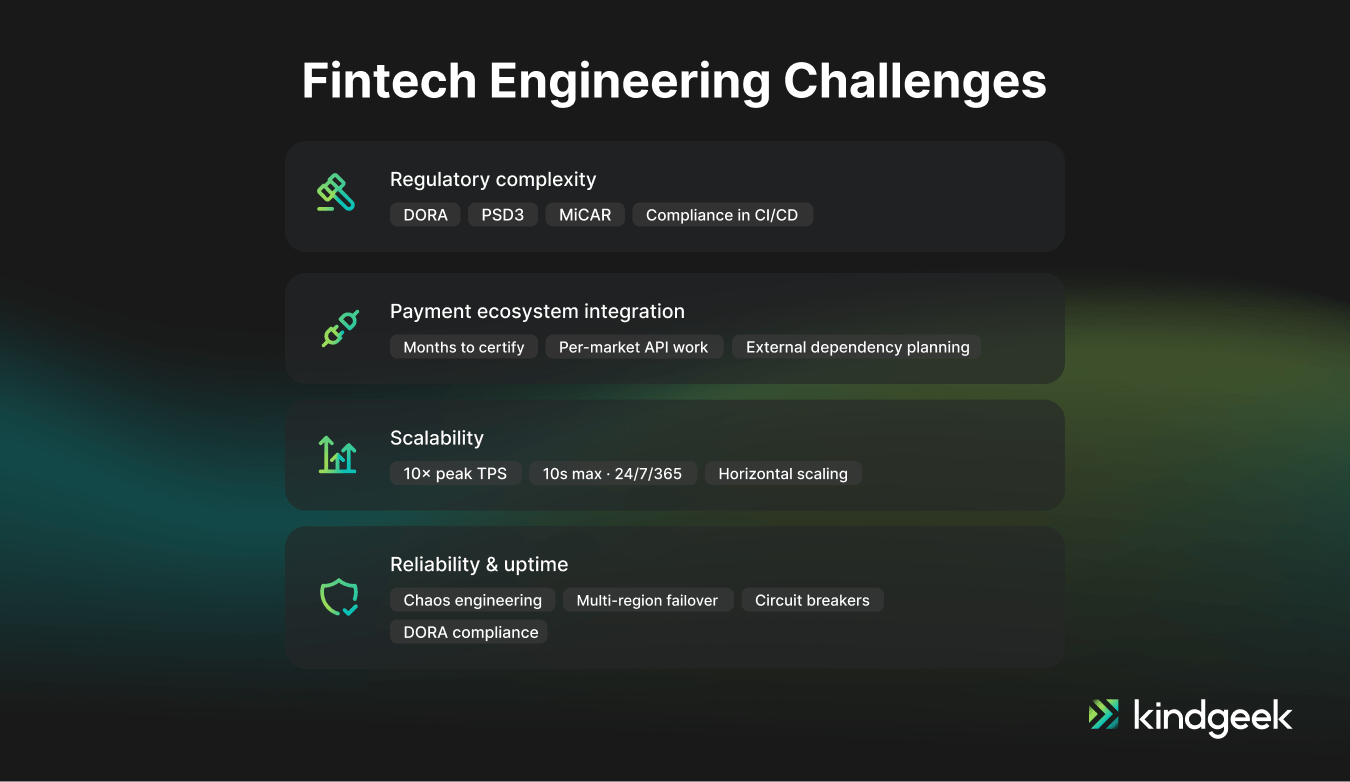
Regulatory and Compliance Complexity
The EU regulatory environment for financial products comprises several overlapping frameworks that change on differing timescales. DORA entered into force in January 2025, introducing new ICT risk management, incident reporting, and resilience testing obligations for financial entities and their critical third-party providers. PSD3 is progressing through Member State implementation. MiCAR is reshaping the engineering and licensing requirements for crypto-asset products across the EU.
Keeping up with this regulatory change is a continuous engineering activity that requires architects who read regulatory guidance alongside technical documentation and automated compliance testing integrated into the CI/CD pipeline.
Integrating with Banking and Payment Ecosystems
Integration with acquiring banks, card schemes, and open banking APIs is consistently more complex in practice than vendor documentation suggests. Visa and Mastercard scheme certification requires months of technical testing in environments that behave differently from production, and certification timelines must be planned into delivery schedules from the outset. Open banking APIs across EU markets remain inconsistent despite PSD2 standardisation efforts, requiring per-market integration work that compounds rapidly across a target geography. Teams without prior integration experience regularly discover these gaps after committing to delivery timelines, making the presence of experienced engineers a significant risk mitigation factor.
Handling High Transaction Volumes and Scalability
Payment systems experience highly concentrated demand spikes, such as Black Friday events, payroll processing cycles, and real-time promotional campaigns. A system designed for 500 transactions per second may need to sustain 5,000 TPS for short periods without performance degradation. This is typically only achievable through horizontal scaling of stateless services and infrastructure validated through load testing at multiples of expected peak capacity.
The EU Instant Payments Regulation, which came into force in 2024, has raised the bar for scalability and availability for EU-based fintechs. Payment service providers are now required to process euro transactions within 10 seconds on a continuous 24/7/365 basis, significantly tightening operational expectations for payment infrastructure.
Ensuring Reliability and Uptime for Critical Financial Workflows
DORA mandates ICT resilience testing, incident reporting, and continuity planning for financial entities, creating a regulatory obligation around what was previously a commercial best practice. Beyond that obligation, payment infrastructure downtime during business hours generates direct financial loss, reputational damage, and, in regulated contexts, mandatory regulatory disclosure.
Mature fintech engineering teams apply chaos engineering, multi-region failover design, and circuit breaker patterns as standard practice, and they validate these designs through regular resilience testing rather than assuming they function correctly.
Fintech Product Engineering Best Practices
Security-by-Design
Architectural-level threat modelling provides a means to identify attack surfaces and data flows that need to be protected and to make judgements regarding network segmentation, authentication models and encryption needs. All API endpoints must have authentication and authorisation controls. Secrets should be maintained using specialised vaults such as HashiCorp Vault or AWS Secrets Manager and should never be kept in environment variables or version control.
The infrastructure layer must enforce network segmentation instead of the application layer, since application-level controls can be bypassed.
Modular and Scalable System Architecture
With increased regulatory requirements and additional payment rails, monolithic fintech products accumulate technical debt quickly, as each change involves entire system deployments and entails regression risk across unrelated components.
Event-driven microservices allow engineers to scale and evolve specific payment processes, such as authorisation, clearing, and settlement, independently and upgrade them without releasing the entire system. Modularity is especially useful for goods that need to add payment method support or roll out new regulatory features on timescales dictated by external demands rather than internal roadmaps.
Automation of Compliance and Testing
Compliance checks must run in the CI/CD pipeline and execute with every deployment, not through occasional manual audits. Policy-as-code tools evaluate infrastructure configurations against PCI DSS and GDPR requirements before they reach any environment.
Structured, tamper-evident logging, in which every transaction event has a uniform model with timestamps, agent names, and result codes, cuts audit reaction times from days to minutes and gives regulators and internal audit teams the proof they need.
Performance Optimization and Low-Latency Design
Payment flow performance SLAs should be set during the architectural phase and evaluated on a continual basis via the CI/CD pipeline. You set p95 and p99 latency goals for each payment flow and conduct automated load tests against those goals on every deployment, catching regressions before they reach customers. An 800ms payment authorisation in production is an architectural fault that multiplies under stress, and fixing it after release is a lot more costly than avoiding it in design.
Technology Stack for Fintech Product Engineering
Technology selection in fintech engineering depends on latency requirements, compliance control capabilities, and the availability of fintech-specific tooling within the ecosystem. The right stack is the one that satisfies these constraints for a given product type, not the one that reflects the team’s prior preferences. The table below shows the standard technology layers and the rationale behind common choices:
| Layer | Technologies and Rationale |
| Backend | Java/Kotlin (Spring Boot), Go, Node.js: chosen for concurrency, throughput, and fintech ecosystem maturity |
| Cloud | AWS (GuardDuty, Macie, CloudHSM), GCP, Azure: PCI DSS and DORA-aligned configurations required at provisioning |
| Messaging | Apache Kafka for event streaming, RabbitMQ for task queues, Redis for session and rate-limit state |
| AI and ML | Fraud scoring models (XGBoost, LSTM), LLM-powered KYC document verification, anomaly detection pipelines |
| Data | PostgreSQL/CockroachDB for transactional workloads, Snowflake/BigQuery for analytics and regulatory reporting |
| Observability | OpenTelemetry, Datadog, Grafana: PII-safe logging required by GDPR Article 25 at all layers |
Artificial intelligence has become a standard component of fintech product engineering. Its primary applications include fraud detection, KYC document verification, and credit risk modelling, which tier-1 fintech companies now use extensively across production systems. As these systems mature, companies increasingly adapt them to regulatory expectations around AML and fraud prevention, positioning AI not just as a performance enhancer but as a functional requirement in modern financial infrastructure.
How to Build a Fintech Product Engineering Team
Engineering Roles for Successful Fintech Product Development
A complete fintech engineering team covers six distinct functional areas. General software development teams typically cover three of them, with the gaps concentrated in the areas most likely to generate compliance failures and delivery delays.
| Role | Responsibility | Note |
| Fintech Solutions Architect | System design, integration topology | Domain-specific patterns are critical; generic architects miss them |
| Backend Engineers | Core transaction logic, API layer | Fintech experience shortens delivery by approximately 30% |
| Security/Compliance Engineer | PCI DSS, pen testing, SIEM | Non-negotiable in any regulated product environment |
| DevOps/Platform Engineer | CI/CD, cloud infrastructure, secret management | Builds the reliable deployment pipeline behind the product |
| QA/Performance Engineer | Load testing, chaos engineering | Validates SLA commitments before go-live, not after |
| Product/Delivery Lead | Roadmap, stakeholder communication | Aligns technical decisions with regulatory timelines |
Domain Expertise
Fintech engineers who have shipped a PCI DSS-compliant card issuing platform can apply tokenisation architecture, scheme certification workflows, and SCA exemption logic to design reviews and implementation decisions from day one. A generalist engineer researching these criteria for the first time on the project will add months to the delivery timetable in technically difficult and compliance-critical areas.
When architects, security engineers, and QA experts share domain expertise, design reviews uncover compliance gaps and architectural issues before production, when remedial costs are orders of magnitude greater.
In-House Team vs. Fintech Engineering Partner
Building a fully productive in-house fintech engineering team typically takes 12 to 18 months. Hiring engineers with domain-specific expertise in payment infrastructure, regulatory compliance, and financial data architecture is both difficult and highly competitive.
A fintech-specialized engineering partner already has this expertise in place. As a result, companies can often begin productive delivery within 6 to 8 weeks instead of spending months building a team from scratch. That makes the partnership model especially advantageous for firms launching their first or second regulated product on a fixed timetable.
The question is where you get domain expertise most efficiently. For teams building differentiated product features, in-house capacity is valuable; for the compliance-critical infrastructure layer that all fintech products share, a specialised partner reduces both timeline and delivery risk.
Fintech Product Engineering Use Cases
Digital Banking Platforms
Digital banking products, whether neobanks or banking-as-a-service propositions, require core banking integration, real-time account management, automated regulatory reporting, and consumer-grade mobile UX, all built on a stack that satisfies EMI or banking licence requirements.
According to Research and Markets, the global neobanking market grew from $261.4 billion in 2025 to $385.05 billion in 2026. Europe dominated with approximately 34% of global market share in 2025, driven in part by PSD2 open banking infrastructure that lowered the barriers to digital-only banking entry.
Payment Processing Solutions
PSP and acquiring platforms handle card acquiring, payment routing, settlement, and chargeback management. These systems operate under PCI DSS Level 1 and scheme certification requirements, with sub-second authorisation as a baseline operational expectation.
Building these products correctly requires engineers who have navigated scheme certification, managed reconciliation discrepancies at scale, and designed idempotent transaction flows that survive network failures. Kindgeek’s approach to financial API integration illustrates how these connection layers are structured to maintain reliability and compliance across multiple acquiring and banking partners simultaneously.
Lending and Credit Platforms
BNPL, consumer credit, and SME lending products require credit decisioning engines, loan origination workflows, and compliance with consumer credit regulations. Recent updates to the EU Consumer Credit Directive have also introduced stricter affordability assessment requirements for these products.
AI-driven underwriting models reduce manual review rates substantially in mature implementations, and their explainability requirements under EU AI Act provisions introduce a new engineering constraint that lending platforms must address in their model governance architecture.
Wealth Management and Investment Apps
Robo-advisors and retail investment platforms operate under MiFID II suitability requirements, maintain comprehensive records of order execution, and integrate with brokers and custodians through proprietary APIs or the FIX protocol. Their core engineering components include low-latency market data pipelines, portfolio valuation engines, and regulatory reporting modules. MiFID II best execution obligations also require firms to preserve audit trails of order-routing decisions in immutable logs.
Embedded Finance Products
Embedded finance – the integration of payments, credit and insurance services into non-financial applications using Banking-as-a-Service (BaaS) infrastructure – has become a major growth area in financial services. The expansion is part of a bigger move to supply modular financial services via APIs, instead of discrete solutions.
From an engineering perspective, these systems rely on clean API abstraction layers over regulated payment infrastructure, configurable white-label compliance controls for different partners, and BaaS architectures that enable non-financial companies to offer regulated financial services without holding their own licences.
How to Choose a Fintech Product Engineering Partner
Selecting an engineering partner for a regulated financial product requires the following attributes:
- Demonstrable, referenced experience with PCI DSS, PSD2, DORA, and relevant licensing frameworks across completed, shipped products in production environments.
- In-house compliance and security engineering capability rather than reliance on external compliance consultants brought in at the end of the build cycle.
- Quality certifications: ISO 9001 for process and quality management and ISO 27001 for information security management, both of which indicate audited, repeatable engineering processes.
- Capacity to grow the team without diluting domain knowledge. This often needs an enterprise with a big enough bench of fintech-experienced engineers to staff new streams without retraining generalists.
- A partnership model oriented toward long-term outcomes rather than time-and-materials delivery, because fintech products require ongoing compliance maintenance as regulations change.
Build Your Fintech Product with an Experienced Engineering Team
Fintech products succeed when engineering teams carry domain knowledge that enables them to anticipate regulatory requirements, design for the failure modes that financial infrastructure encounters, and make architecture decisions that remain sound as the regulatory landscape evolves.
Kindgeek is a fintech software development company with 200+ engineers, ISO 9001 and ISO 27001 certifications, and a track record across fintech software development spanning card issuing platforms, PSP infrastructure, digital banking products, and embedded finance solutions across 12 EU markets. 70% of clients come from referrals, and the average engagement runs more than two years, reflecting a partnership model built around production outcomes.
Ready to engineer your fintech product?
Kindgeek engineers have shipped PCI DSS-compliant card issuing platforms, payment infrastructure processing billions in transactions annually, and digital banking products across 12 EU markets. Contact us to discuss your technical requirements.
Contact usHow does fintech product engineering differ from standard software development?
Regulatory compliance, financial data integrity, and security architecture are the major technical constraints driving every design choice in fintech product development from the outset. General software development usually treats these problems as secondary needs or as post-build enhancements. The practical difference shows up in places such as PCI DSS network segmentation, PSD2 Strong Customer Authentication logic, and immutable audit logging, all of which involve basic design choices that are hard to retrofit into an existing system.
How long does building a fintech product take?
A PCI DSS-compliant payment gateway with basic acquiring capabilities can reach production in 4 to 6 months with an experienced team. A full neobank with EMI licensing, card issuing, and open banking integrations typically requires 9 to 18 months, with the range driven largely by licensing timelines and banking partner onboarding. The most common cause of delays is underestimating the time required for compliance activities, scheme certification, and third-party integration testing.
What compliance frameworks do fintech products typically need to meet?
EU-regulated fintech products typically operate under PSD2/PSD3, GDPR, PCI DSS, and DORA. Crypto-asset products must also address MiCAR, and consumer lending products fall under the EU Consumer Credit Directive. A properly structured discovery phase identifies all applicable frameworks at the outset and implements them as architecture constraints throughout the build.
Can a general software agency build a fintech product?
A generic software agency can make a fintech product, but the lack of subject expertise raises the delivery risk and the overall cost. If the project is the first time that engineers are dealing with fintech-specific standards, they will need to investigate and put them in place throughout the engagement, lengthening deadlines and the risk of compliance gaps. The cost of the rework that is needed to fill such gaps after the first development is generally more than the cost of the difference between a general agency and a fintech-focused team.
What does compliance-by-design mean?
Compliance-by-design implies that you take relevant regulatory frameworks into account in every technical choice from the very beginning. PCI DSS scope requirements impact network design; GDPR data residency requirements dictate where databases are provided, and automated compliance tests are executed in the CI/CD pipeline on every deployment. When compliance is evaluated only at the end of the development cycle, findings often necessitate architectural changes rather than incremental configuration fixes.